Adding Feide login to a service#
The process for adding Feide login to a service varies greatly between different services. Some services have built-in support for federated login / single sign on that can be used with Feide. Other services may required you to add a custom authentication plugin.
Protocols#
Under the tab configurations you add configuration so that the Feide-system is able to communicate with the service. Feide supports two different authentication protocols:
Some services only need a single configuration, while others may need separate configurations for each organization with access to the service.
Factors that may affect your choice of protocol is:
The OpenID Connect protocol in Feide is available for users from organizations that are connected to the newest version of Feide. Over 97% of all organizations that are connected to Feide are on the newest version including all the municipalities and county municipalities, but there are still a few organizations that do not have access. For an overview of which organizations have “OIDC” enabled, see q.feide.no
Existing support in applications / frameworks: Some applications and web frameworks have built-in support for one of the protocols. In that case, it is usually easiest to use the protocol already supported.
Support for logging into mobile applications: The OpenID Connect protocol is simpler to use when logging into mobile applications. Using this protocol, you can now choose not to require a new login after eight hours, but leave the user logged in for a longer period, in line with what end users often expect from mobile applications today.
Using the OpenID Connect protocol allows your mobile application to directly get an OAuth 2.0 access token, that can be used to access APIs.
Using OpenID Connect a service can retrieve information about teachers and students in a group, without each student having logged in beforehand. For primary school, secondary school and upper secondary school retrieve information about grade level (Grep), courses, basis groups, teaching groups and possibly other groups. For Universities and university colleges the group data is from FS (Common Student System), which provides information which class, class, study program, field of study and subject affiliation
Complexity of the protocol: The OpenID Connect protocol is in general simpler than the SAML 2.0 protocol.
Do you service need to identify and authenticate international users or people outside the education? When using OpenID Connect a service can enable other login providers in addition to Feide login like ID-porten, eduGain and eIDAS. Read more about login providers when using OpenID connect.
Integration methods#
Depending on the software used to implement the service and the architecture of the service, there are several methods that can be used to integrate the service with Feide.
Some software or software frameworks may already have support (either directly in the software or through plugins) for SAML 2.0 or OpenID Connect.
In some cases, authentication can be handled by a web proxy that runs in front of the software. This proxy can perform the Feide-authentication and pass user data to the application through request headers.
You can add support for Feide directly into the software. If you go for this solution, we strongly encourage you to use existing libraries that implement the SAML 2.0 protocol or OpenID Connect protocol. This is because the protocols can be very complicated, especially the SAML 2.0 protocol.
Adding Feide login to the service#
Once you have decided on a protocol and integration method, you can add Feide login to the service. The exact method for performing this depends on the software, frameworks and libraries used. Please refer to the documentation of the relevant software for details about how to configure a SAML 2.0 / OpenID Connect integration.
In general it will be something like the following:
Add any required plugins/components/libraries to the service.
Configure the software to connect to the Feide login system.
For SAML 2.0 services, this is typically done via SAML 2.0 metadata. For Feide we have to SAML 2.0 metadata available, for the test system and the production system.
For OpenID Connect, we do not have a separate test system. but you can test without publishing the service. The OpenID Connect configuration is available in OpenID Connect Discovery format from our login system. If the software supports OpenID Connect Discovery, you can configure the software with the following
Issuer, and it should automatically fetch the required configuration: https://auth.dataporten.noDetermine what attribute groups your software needs to work.
The user information is transferred to the service as attributes groups in the login response. The software can typically make the attributes groups available to your service in various ways.
Think about what information the service needs to know about the user and host organization. Avoid requesting access to more information than the service needs to work. Some services only need to log in to ensure that there is a person associated with the education sector, while others need more to personalize the service for the user. If you find out later that the service needs more information about the user, you can add more attribute groups.
For an overview of available attributes, see the section about our attribute groups.
Registering the service in Feide#
Once you have decided on a protocol and integration method, you can register the service in the Feide customer portal.
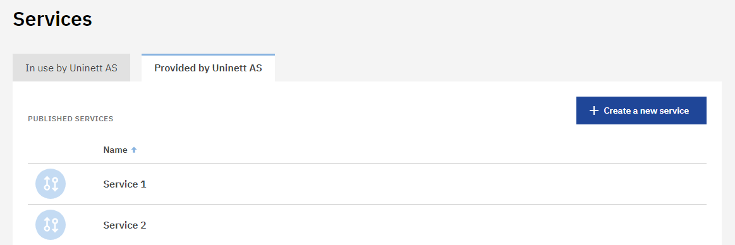
Screenshot of services provided by the organization
When registering a new service, the steps of information that need to registered is showed in the left side under “Prepare for publication”. You need to fill out the required filed that are marked with * to publish the service. Other details that are not required are optional to register but can be useful for the administrator at the host organizations and end users.
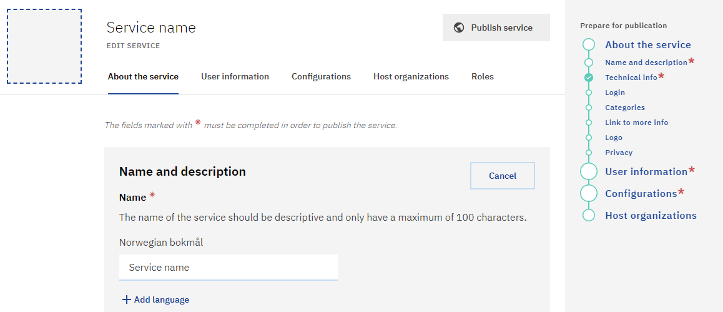
Screenshot of registering a new service
Adding information about the service#
Under the “About the service” tab you add details about you service. Take special care to fill in understandable details about your service, including name, description, logo and more. This information will be displayed to end users during login and on our overview of services with Feide login.
Selecting user information#
Under the “User information” tab you select which information the service needs to receive about the end user and the host organization, there you can choose what information the service should try to collect about end users as they login with Feide. The availability of the information depends on whether it exists in the host organizations user directory. The information is defined in the attribute groups and for an overview of available attributes, see the section about our attribute groups.
Some of the attribute groups is by the general public and Feide considered as semi-sensitive information. Those attribute groups are only released to service that actual need it to make a better service and/or can’t user other information. Therefore, it can only be added to a service by Sikt. Send an email to kontakt@sikt.no and explain why the service requires this attribute group, and why it is not enough with another available information through Feide.
Beware that some attributes groups and attributes in attributes groups are only available with SAML configuration or for OIDC configuration.
Adding configuration#
Under the “Configuration” tab you add configuration/configuration to the services so, the Feide-system can communicate with your service. Some services only need a single configuration, while others may need separate configurations for each organization with access to the service.
Feide supports two different authentication protocols: SAML 2.0 and OpenID Connect/OAuth.
If you are integrating with OpenID Connect/OAuth protocol you can enable other login providers in addition to Feide login like ID-porten, eduGain and eIDAS. This is done for service that need to identify and authenticate international users and/or people outside the education and not only users with Feide users. Enabling other login providers is done when adding or editing the OIDC-configuration. Read more about login providers when using OpenID connect.
If you have configuration that need to be moved for another service registered under the same organization, you can move them your self-clicking “Move configurations” under the more menu (…) for the specific configuration. If the configuration needs to be moved across service provider contact us at kontakt@sikt.no, and we will move configuration to the right service provider for you.
Testing the integration#
When the service is registered in Feide, you can test the integration before publishing it. For information about the test users, including how to access them, see our documentation about test users.
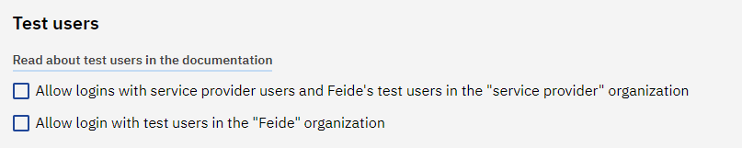
See “logging in using test users” for information about how to log in using test users.
Be sure to disable Feide test user before you move your service to a production environment.
How to enable Feide login#
If your users are students, researchers, teachers or other employees in Norwegian education, you probably want to enable Feide login. In the Feide customer portal., you can enable which organizations or individual school that get access to activate the service when editing the service.
When a service is published, the organizations that should have access, must be granted access. After access have been granted, each individual organization must actively choose to activate the service.This is done in Feide’s customer portal by a Feide administrator at the host organization. There they can search for the service by; the name of the service, name of the service provider, and/or service description. After the service has been activated by the organization it will be an option in the Feide login for the user and the user can login to the service.
Do your service need to identify and authenticate international users or people outside the education? When using OpenID Connect, a service can enable other login providers in addition to Feide login. This is done under “configuration” tab. More information about login provider available at OIDC configuration.
NB! Feide is an opt-in this means that before an organization can use a service, you as service provider need to give access and the organization must activate login to the service before the service is available for the user at the organizations.
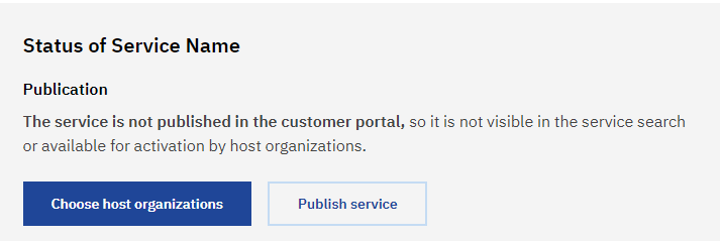
Screenshot of publishing the service
You can remove the service and we recommend that all service that are no longer in uses get removed for a better overview of available services.
If you are still testing the service, we recommend that you unpublish the service or removes the services from public list and API. If you choose to unpublish the service is no longer available in the service search for the host organizations and cannot be activated. If you only removed the service for public list and API the service gets removed from list like the list of available services in Feide but is still available in-service search.
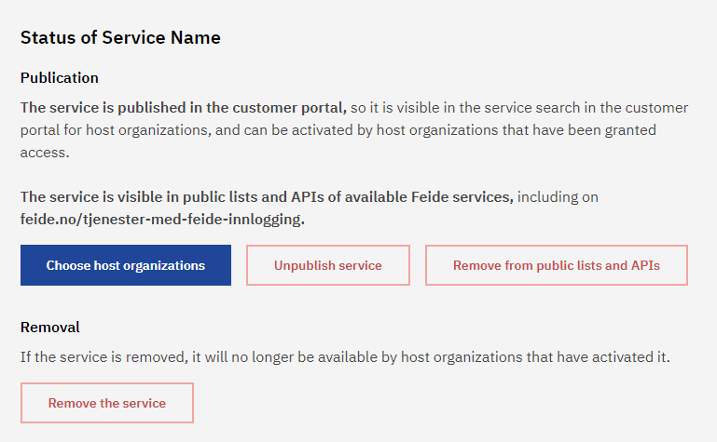
Screenshot of status of the service